In Part 1 of this series, I wrote about how a beginner might want to approach the field of cybersecurity, and the knowledge and skills they should seek to acquire. In this article, I want to address the folks that have been working now for a couple of years and are seeking to get to the next level.
Typically, someone with 2 years of experience in cybersecurity would have spent most of those two years working in one of the following sub-domains:
1. Pen-testing
2. Advisory and/or audit
3. Security operations center
4. Digital forensics
At the 2-year stage, a key choice presents itself. Should you continue to specialize in the same field or should you look to diversify your interests. Either choice is valid and boils down to an individual’s own preference. In the next section, I lay out the pros and cons of either choice.
Specialization vs. Generalization
It may be the case that you are thoroughly enjoying your work within one of the four sub-domains listed above and would like to continue working in the same domain. If so, then you should ideally seek to get to the next level within the same sub-domain (see specific sections later in this article). You should also seek to acquire a well-recognized certification relevant to that sub-domain. The advantage of continuing to grow within the same domain are that you would soon be reaching a stage of expertise and this is always going to be a good thing, no matter where you go next.
Another alternate is to look to shift to a different sub-domain and spend a couple of years in that. Often, I have seen people with 2–3 years of experience hesitate to learn a different domain primarily from the fear of failure. Having done pen-testing work for a couple of years, it seems alien to now want to shift into compliance and audit related work. In my view, a generalist will eventually do better in their career than a specialist. The risk of being a super-specialist are that you may be left redundant when a tool is created that does the bulk of what you have been doing so far. By becoming a generalist, you not only de-risk your career being automated from under your feet, but also become more valuable as someone who can bring different perspectives to the larger domain of cybersecurity.
Someone who can evaluate a network diagram, review a firewall configuration, and audit a change management process, while being able to articulate the business risk from insecure firewall rules is a very valuable asset to any organization. Similarly, someone who is a forensics investigator but has had prior experience in pen-testing would be able to imagine an attacker’s modus operandi more easily than someone who does not know what the cyber kill-chain is or how lateral movement takes place.
So, I think the key question to ask yourself is — are you resisting from expanding your portfolio because you are loving what you are doing, or because you are afraid to come out of your comfort zone. If the answer is that you absolutely love what you are doing, then read on.
Career Progression
In the next few sections, I list out the next steps you should seek to accomplish within each of the 4 sub-domains listed above.
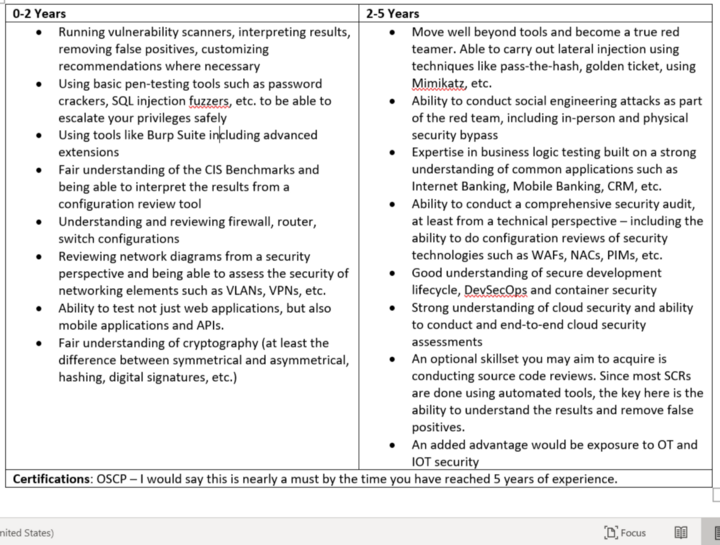
Pen-Tester to Red Teamer
After a couple of years doing vulnerability assessments and penetration testing (VAPT) projects, you would have acquired a fair bit of skill in using the right tools, interpreting their results and using limited exploitation techniques to penetrate deeper into systems. You may even have, once in a while, gained Domain Admin access within the network you were testing. However, you would typically struggle to get that level of success within a hardened environment. Here’s a summary of where you should be at this stage and where you should aspire to get to in the next two years of your career:
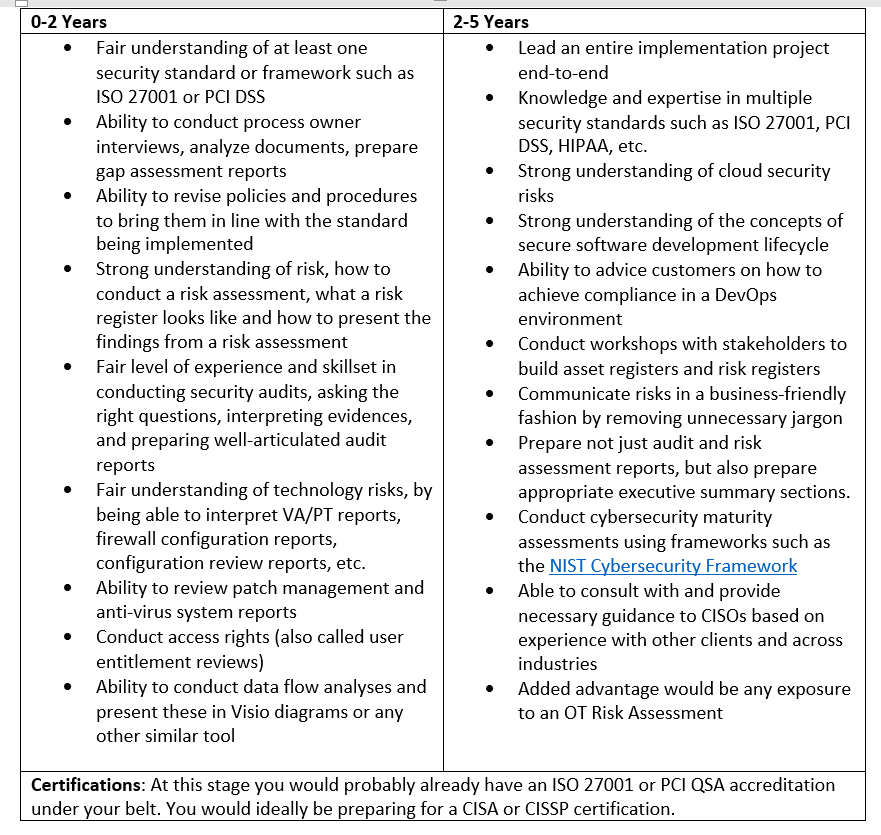
Analyst to GRC Consultant
If you have spent the first two years of your career in the compliance and advisory sub-domain then you have most likely done 20–30 engagements covering different frameworks such as ISO 27001:2013, HIPAA, PCI DSS, etc. It may be the case that you have joined a team or a company that specializes in one of these and most of your experience now is restricted to that domain, but now would be the time to expand your horizons.
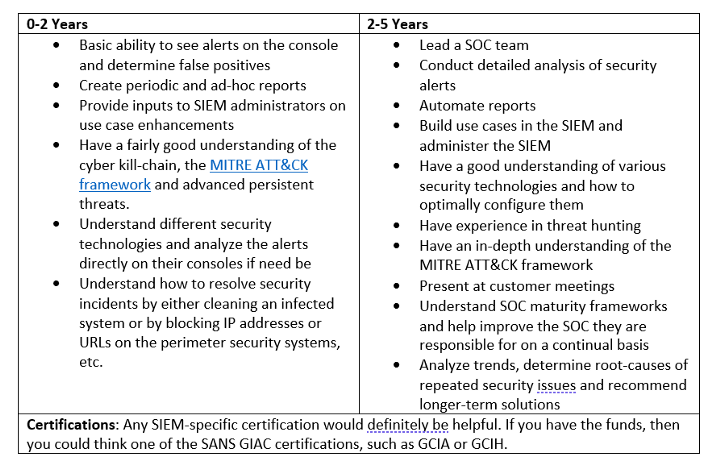
SOC Analyst to SOC Manager
Within a Security Operations Center, there are many different teams. There’s the security monitoring team consisting of L1 and L2 analysts, reporting into a Shift Lead. There’s the SIEM administration team that’s focused mainly on adding new log sources to the SIEM, building new use cases, etc. There’s a threat intelligence team that integrates multiple threat feeds, releases advisories, etc. An incident management team that investigates incidents, guide the IT teams to patch systems or block IP addresses, etc. and accordingly closes the reported incidents. There’s probably also a small automation team that continues to automate use cases and reports. I would strongly encourage all SOC team members to constantly seek to join these different teams or shadow their friends in the other teams and learn as much as they can. This will give them the ability to lead a larger SOC team within a Managed Security Service Provider or even head the SOC for a large organization.
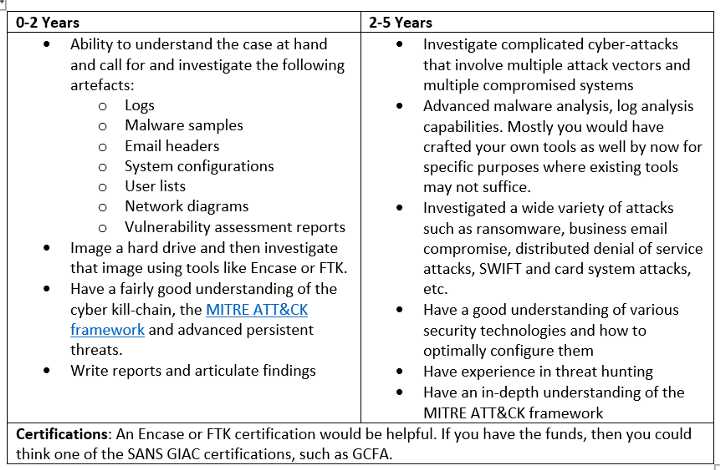
Forensics Newbie to Expert Investigator
Personally, I find security incident investigation to be one of the most fascinating aspects of cybersecurity. Having worked across the different sub-domains over the years, I still get fairly excited when one of our teams is digging deep into an interesting cyber attack. When starting out, you may either get involved in live forensics or offline forensics. Both are equally important, so don’t ignore one for the other. There are numerous circumstances where disk imaging and offline analysis are simply not feasible, and you have to use the right tools and techniques to conduct investigation on a live system.
General Areas of Improvement
Besides the sub-domain specific areas listed above, the following are general areas in which you should have significantly improved yourself in the 2–5 years duration
People skills. As you grow in your career, the mix between executing projects vs. managing people will continue to change. In the initial few years, you will be almost completely focused on executing projects. But from the 2nd and 3rd year onward, you will definitely get additional responsibilities to mentor new team members, lead teams, coordinate projects, etc. Most techies would resist this aspect, but you should be clear if you wish to be a single contributor for your entire career or you would like to take up the managerial responsibilities. Either ways, you must then communicate this to your management and ask to be given those types of roles. The large majority of organizations that you work in would not have the facility to allow you to continue working in a technical role without taking on any managerial responsibilities. So, make your decisions wisely as this can have long-lasting impact on your career. My 2 cents would be that for most of us it is best to start honing up our people skills and project management skills after the 2-year period, as this is what will help us move up the hierarchy.
Report writing. Your reports by now should be concise, easy-to-understand, and have a logical flow. You should be able to draft very good Executive Summaries as well.
Customer communication. Whether it is ongoing project-related communication or presenting the final reports, you should be able to do these with ease. One sign that your communication skills have improved is if you are able to deliver training programs on an advanced topic within your sub-domain.
In conclusion, whether you choose to stick to your sub-domain and specialize in it or you choose to switch sub-domains and become a generalist, you must be a student for life. And besides continuing to work on your technical knowledge and skills, it also becomes imperative that you improve on your non-technical skills as well. Finally, it is the team that carries the day through, and learning to work well within a team can potentially give you a higher level of success than being a solo performer.
Source: The blog “Cyber security Career Guidance — Part 2 — the Intermediate Level’ was published on Medium.com on September 11th 2020, by our Founder & CEO KK Mookhey.

