What is a Spear Phishing?
Spear phishing is a deceptive communication technique in which a victim is lured via e-mail, text or tweet by an attacker to click or download a malicious link or file. The common objective of this technique is to compromise the victim machine by stealthily inserting a backdoor which seeks to obtain unauthorized access to confidential data remotely. These attempts are more likely to be conducted by attackers seeking financial gain, trade secrets or sensitive information.
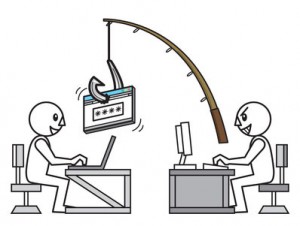
Popular Techniques used for the Spear Phishing attack comprise of mixture of social engineering, client side attacks, and requests via social networking sites etc.
What is difference between a Phishing and Spear Phishing attack?
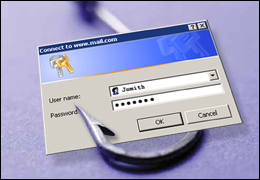
Phishing messages appear to come from large well-known company or web site having a large user base such as Facebook, Twitter, Amazon, Paypal, BestBuy or eBay. However, in spear phishing, the apparent source of the e-mail is likely to be an individual generally in a position of authority within the organization.
Most people are conditioned to ignore suspicious looking email asking for confidential information. They simply delete such phishing mails or set filters to do so on automatic basis once they recognize the pattern. Spear phishing is more dangerous than normal phishing because the message seems to originate from a known trusted source, there is information in message supporting its validity, and the request appears to form a logical basis.
Necessary factors for successful spear phishing attack:
- The message should come from a known source or ideally from trusted “highly placed” authoritative figure in organization
- The message must complement the context in what is being said and the contained information supplements its validity
- The recipient can draw a “firm need” or a logical reason for the request made by sender
For a more comprehensive discussion of a Spear Phishing and its testing methodology, view our detailed article uploaded here
”Spear Phishing Testing Methodology” or view PDF version of article below:
