Summary of the presentation and research done – By Hugo Teso
According to Teso, there are two sub-parts when it comes to aviation systems and understanding them.

Concorde airplane or the airplanes of its time used to have all analog systems on-board and were highly isolated from the outside entities. Due to this there are hardly any or no vulnerabilities with respect to information technology.
Teso describes this as an outdated technology which is only used at present as a back up for the new ones and is diminishing with time. As per him the communications used to happen through radio(VHF) and the navigation was carried out manually by plotting charts and carrying out flight planning with the help of ground radio stations.
He says there is very little room to research on this part of the module and concentrate on what is been in use now and have a better understanding.
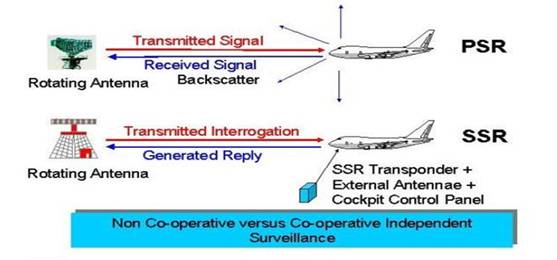
He also mentions about basic working of a radar which is depicted in the below diagram
FYI : PSR (Primary surveillance radar) is used to detect aircraft in sky by a ground station.
SSR(Secondary surveillance radar) is used for aircraft to aircraft and ground to aircraft communication, it gives information on altitude, callsign and speed of the aircraft.
Digital Systems

Airbus A380 is one of the most sophisticated airplanes ever built. It practically has the ability to take-off,navigate and land all by itself provided the data is fed to the auto-pilot from the FMS and such supporting technology is present on ground too.
The above statement serves as the most secured when talking about aviation but is too dangerous when we imply information security on it.
“Complete safety does not mean you are secured”
They are broken down in 3 parts:
The objective is to understand the above technologies and find loopholes in its infrastructure and exploit it. Teso says it is not very difficult as none of the above have any implications towards security, they are all openly transmitted without any mode of encryption used.
It is easier for the attacker or even a person who has little knowledge about the systems to intercept and perform a devastating scenario.
A Brief Summary Of The Attack
- The Discovery Phase: Any aircraft with an ADS-B OUT facility is vulnerable to this phase, in simple terms when an aircraft turns this instrument on, it transmits data of it position and flight to the ground station but since this data is not encrypted in any form it is easily interpreted by any receiver which is able to receive at that particular band of frequency.
The way ADS-B works is that it transmits its data to the satellite above and which relays its information on the ground and the same can be stored or passed in data form if anyone has the receiver.A classic example is a app made for Android and MacOSx called flightradar24. The app has a central receiver which fetches the data and is transmitted to anyone who is using this application over the internet. - Information Gathering Phase: ACARS is a good technology built to outrun VHF and AIRNIC communications.
Its practical use is simply to pass on the information which is useful to pilots.
For eg: During 9/11 attacks all the aircraft flying at that time were alerted using ACARS saying “THERE CAN BE POSSIBLE HIJACKING,STAY ALERT.”The way teso used this was just descriptive and from here on he cannot actually show the attack due to security reasons. He simply was able to intercept this information and manipulate using a tool called ACARS decoder for linux.This tool allows to intercept any information passed over the internet and decode it and possibly even upgrade the information and upload it through a dummy ACARS instrument.ACARS information has very large amount of data which is stored in a database and has a real time updating facility. The company who majors this is SITA based in Geneva,Switzerland. They have a worldwide ground data network which updates airplanes when ever required through telecommunication channels.This is how an ACARS message looks like after decoding it with the tool.In this way he was able to get detailed information about an airplane and manipulate it. - Exploitation Phase: Flight Management System is as it sounds manages the flight from chokes-Off to chokes-On phase ie take-off to landing phase.During a normal flight the weight and balance information,navigation information,routing protocols are been fed in the FMS, later it makes sure it follows the path pilot has fed into the system when the airplane is under auto pilot.Since the real time information is taken from ACARS , teso was successfully able to compromise FMS. This was done by flight simulator,ACARS,ADS-B,FMS second hand instruments bought from ebay and a evil mind.He mapped the output of simulator to all the instruments in a real time scenario,the way he did that was using python scripts for integration,since none of this requires any encryption technique he started transmitting this information in a demo live environment.Now since we know FMS takes data from ACARS he was able to get into FMS console and started to veer the path of the flight in air, without a doubt the flight started turning according to his instructions as it was under auto-pilot mode.In this was he way he was able to control the aircraft by simply toying with the instruments. This was identical to the instruments they use in a modern airliner and he claims they are extremely vulnerable.
Recommendations:
- Strong encryption technique
- A pentesting team dedicated for finding such vulnerabilities for the manufacturer company.
- International standard to adhere while using this technology.
- Centralized and regularly updated systems for vulnerable ones.
Reference Links:
✈✈Aviation 101
»» http://en.wikipedia.org/wiki/Portal:Aviation
✈✈ADS-B
»» http://en.wikipedia.org/wiki/Automatic_dependent_surveillance-broadcast
»» https://www.blackhat.com/html/bh-us-12/bh-us-12-briefings.html#Costin
✈✈ACARS
»» http://en.wikipedia.org/wiki/Aircraft_Communications_Addressing_and_Reporting_System
»» http://spench.net/
✈✈FMS
»» http://en.wikipedia.org/wiki/Flight_management_system
»» http://www.b737.org.uk/fmc.htm
✈✈SDR
»» http://en.wikipedia.org/wiki/Software-defined_radio
»» http://gnuradio.org