INTRODUCTION
WhatsApp Messenger is an application used across various Mobile Platforms for instant messaging. It uses the internet to send and receive audios, videos, documents, location details, messages etc.
WhatsApp saves all the message of user onto a database file in crypt form, which means no one could read anyone’s private messages. WhatsApp uses crypt2, crypt5, crypt7, crypt8 to encrypt all the data so that no one could read the messages from the database file. But those very same files can be easily decrypted without a key.
Steps to Perform WhatsApp Database Extraction With Android
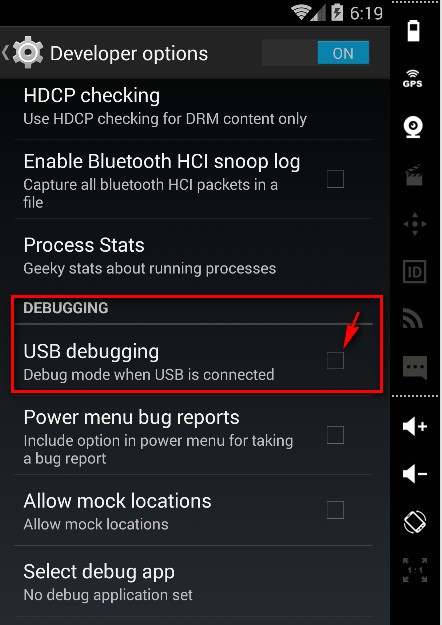
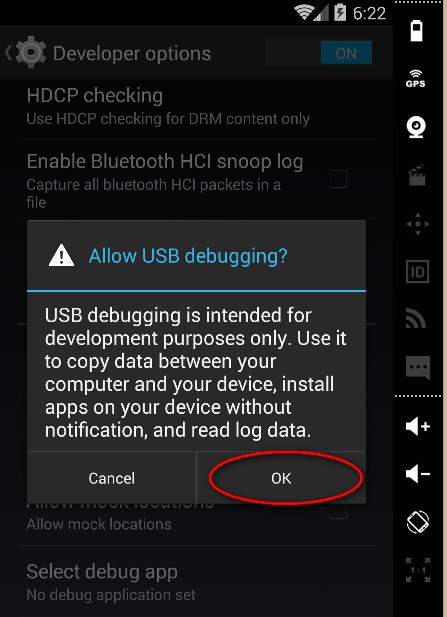
Step 1: To use adb, first we need to enable the USB Debugging feature under Setting -> Developer options on the device.
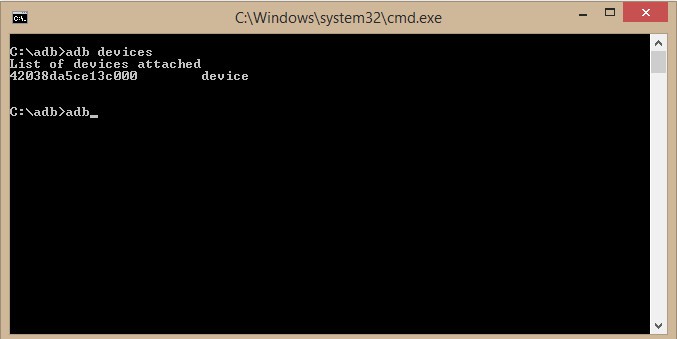
Step 2: From the command prompt, we can initiate the connection with the android device with ‘adb devices’ command.
Step 3: Download any WhatApp version between 2.11.4xx range and degrade your preinstalled WhatsApp by installing it using the command as shown below.
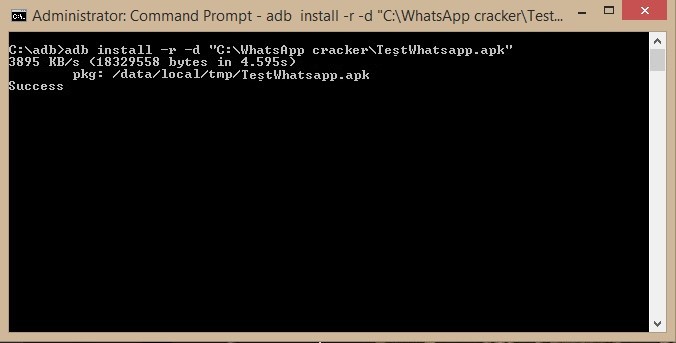
NOTE: Here you are overwriting your WhatsApp application with older one. Once installation is done you will always receive an error as it is an older version of WhatsApp.
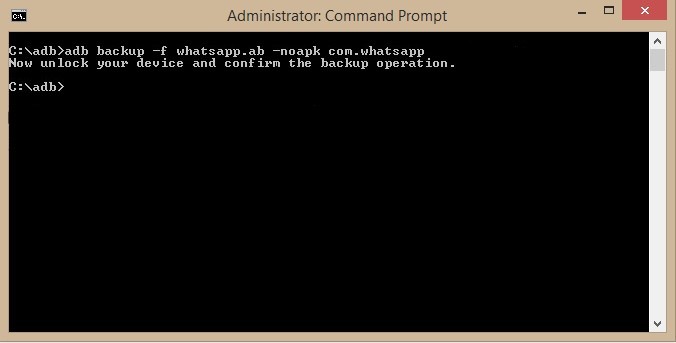
Step 4: Using ‘adb backup’ create a backup file named ‘whatsapp.ab’ from the WhatsApp package that is entitled as “com.whatsapp” on the android devices.
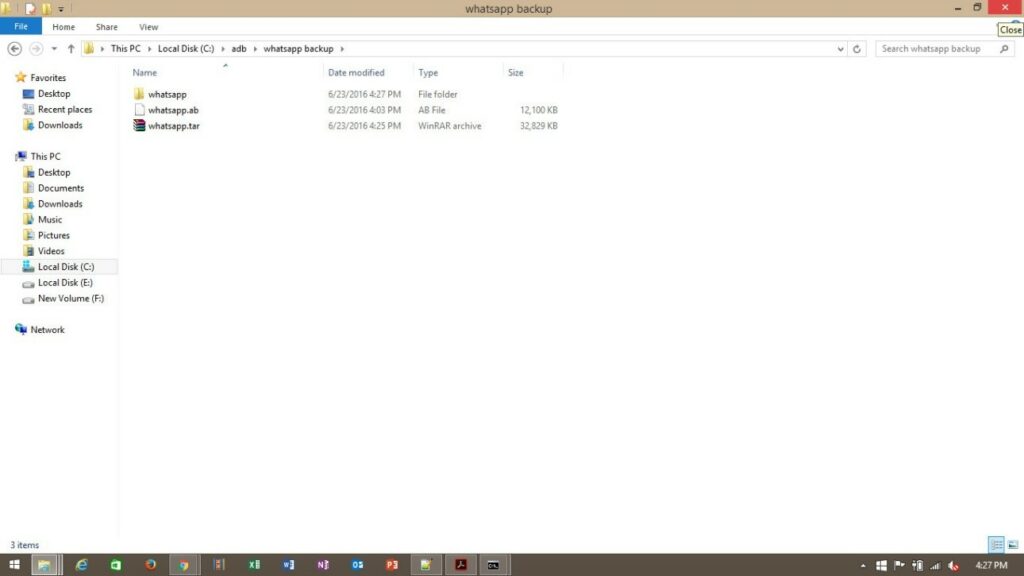
The ‘.ab’ file extension which is shown in the below image is associated with the Google’s Android Debug Bridge (adb) command line utility which is circulated as a part of Google Android SDK that allows the developers to communicate with the android phones through cables. A ‘.ab’ file stores the backup of the device comprising of apps, system data, system settings etc.
NOTE: If any no backup is generated or any error occurs then, go to whatsapp à select ‘settings’ à select ‘chat’ à select ‘backup option as back up on local device’ à Then select ‘Backup’ and wait for the backup to get completed.
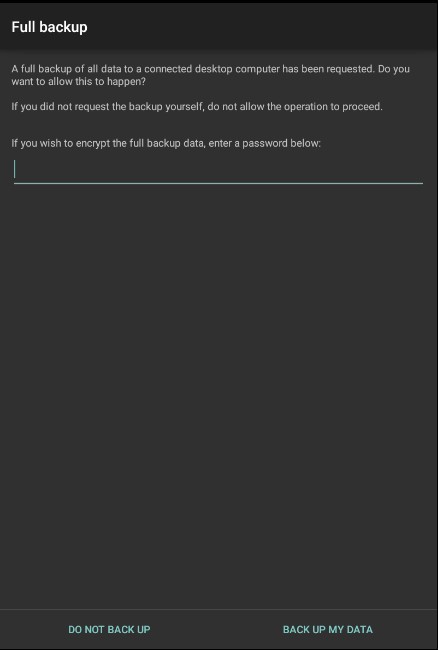
Step 5: Select ‘Back Up My Data’ option on your android device and keep password field blank.
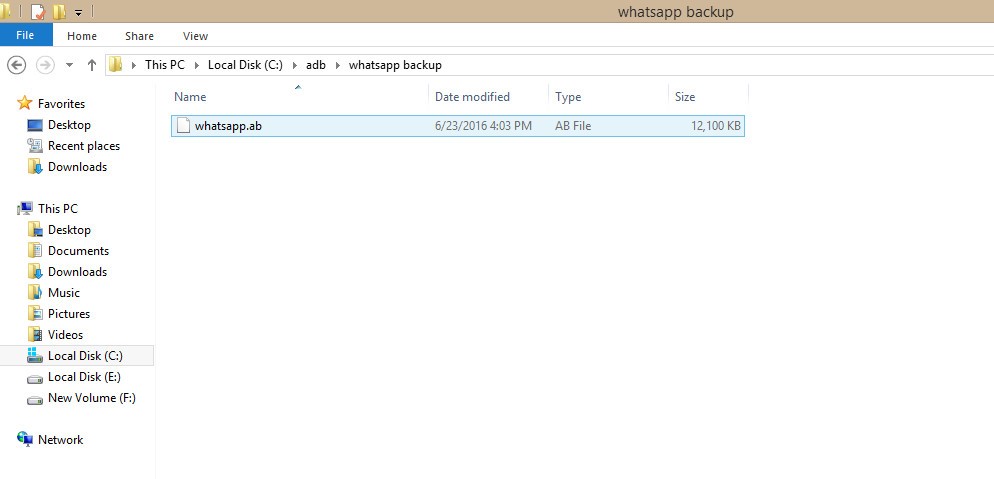
Step 6: Now, a ‘whatsapp.ab’ file is created as shown below:
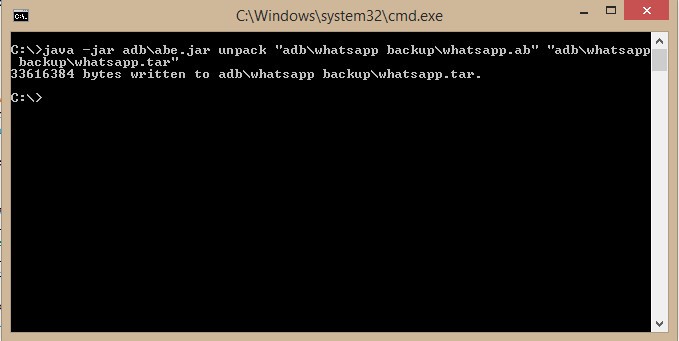
Step 7: ‘abe.jar’ is a utility used to extract and repack the android backup files that are created with the ‘adb backup’ command. We will now extract the ‘whatsapp.ab’ file and name the extracted file as ‘whatapp.tar’ where ‘.tar’ is the archived file containing many other files.
Step 8: Once ‘whatsapp.tar’ file is created, then extract it with WinRAR (or ‘tar -x’ command in Linux).
Step 9: After extraction completes, a folder named ‘whatsapp’ is created and following are contents of that folder shown in image.
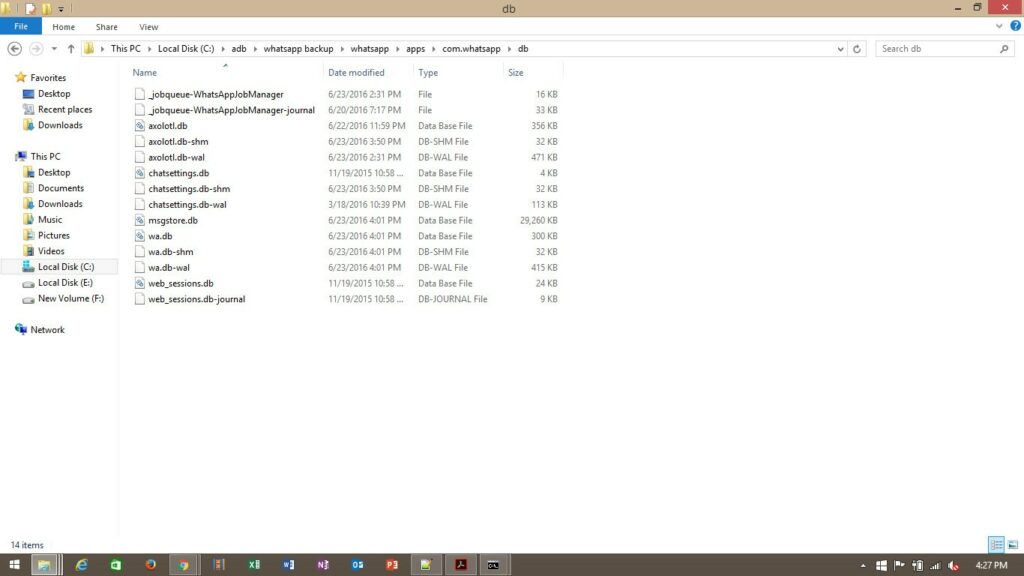
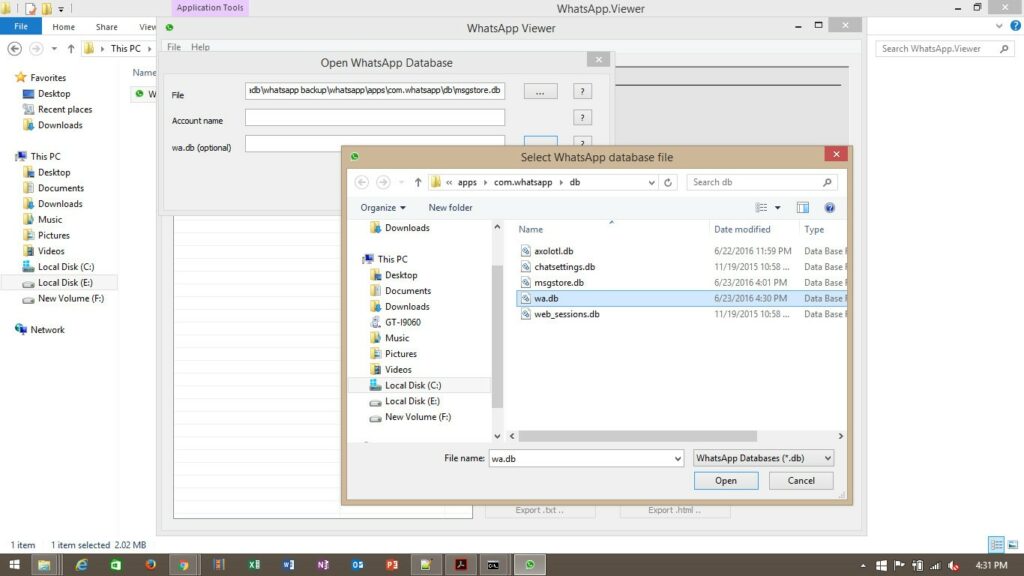
Step10: We are only interested in ‘msgstore.db’ and ‘wa.db’ file. Use a utility called ‘Whatsapp Viewer’ and give the path of ‘msgstore.db’ and ‘wa.db’ as shown below.
Here ‘msgstore.db’ stores all the messages along with attachments and ‘wa.db’ stores all the information related to the contacts.
NOTE: IOS whatsapp database extraction commands are different than that of android. Also after doing the above process, user has to upgrade his WhatsApp from Playstore in order to use it again.
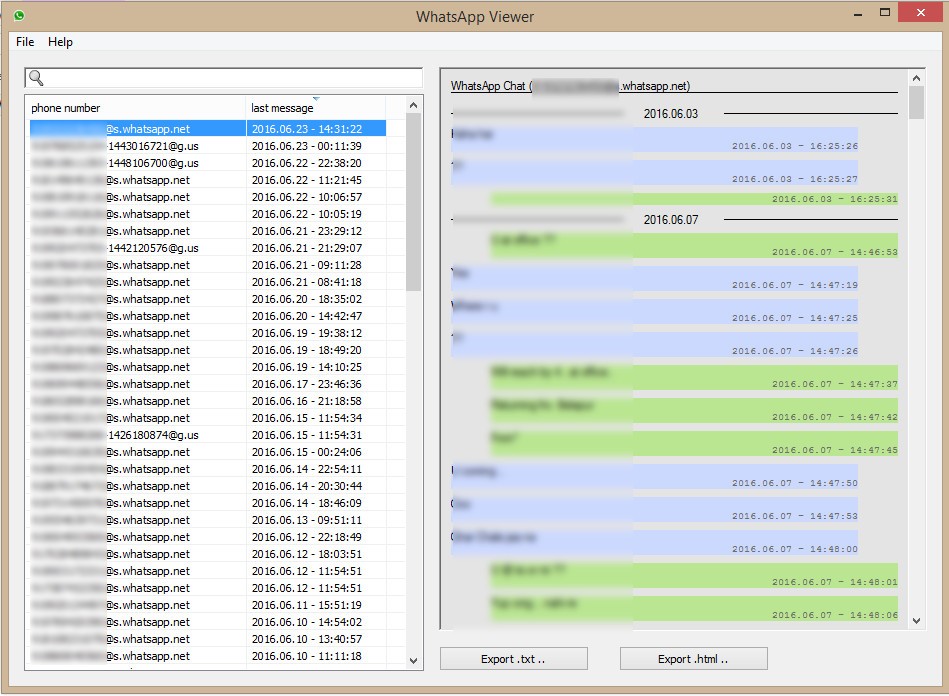
Step 11: Below Screenshot, shows you will see all the chat messages, that were extracted from the database.

Rahil Karedia
This is freak awesome article till the date….. Great share though! Good one young man… Keep going 🙂
abiya
Wonderful bloggers like yourself who would positively reply encouraged me to be more open and engaging in commenting.So know it’s helpful.
INOC | 24x7 Service Desk
Wow! This is a very interesting information. That’s really a clever hack that can be used on things such as investigation. Thank you for sharing this!
Rita
Thank you . But i have problem with a database file in crypt 12 form without key . How can i do ? Could u help me?
Brijesh Zaveri
crypt12 works sometimes.. What’s the problem ?
gopi
how to get adp command
Brijesh Zaveri
Download the android studio or APPIE framework to get adb.
shabby
Hi,
After STEP 4, a whatsapp.ab file is created but of 41B (less than 1KB). Whereas your snapshot shows you got a big size file of 12100 KB.
Please help on this.
Brijesh Zaveri
generally whatsapp creates backup files and those files are the one which we extract through this method. so if there is no backup files in your device, then the chats will not be extracted. That’s why you have 41kb file size.
Michael
This is really really interesting and I will certainly try it out myself, but can you explain the motivation if there is one other than entertainment? Assuming a normal Android user does not have USB debugging enabled, you would have to unlock the phone to enable USB debugging. If you can unlock the phone, you can read the messages in WhatsApp anyway. Am I missing anything?
Brijesh Zaveri
You can connect to the device using adb via device’s recovery mode.
Bradley Host
Highly energetic blog, I enjoyed that bit. Will there be a part 2?|
Nishant
hi, i am also looking for a key to open msgstore.db.crypt12. the peoblem is i don’t have the android mobile and am having it in my laptop. now ow to open it or restore it?
achik
let say i have crypt12 database file without the key file from other phone. Does it possible to decrypt? How to do that?
Amit
My whatsapp account is closed and my phone number no more exist.
Only i have my crypt12 db file, i downloaded it from Google drive.
is there any way to decrypt 12 database file without the key file?
if yes please share.. i have some very important information , which i need to extract ASAP
himanshu
I have my own whatsapp database crypt5 & that same mobile number too. Is there any way to make that database readable without key now ? Please tell .