
Autonomous AI Pen Testing: When Your Security Tools Start Thinking for Themselves
As we navigate the evolving cybersecurity landscape of 2025, autonomous AI penetration testing stands at the fascinating intersection of artificial […]

As we navigate the evolving cybersecurity landscape of 2025, autonomous AI penetration testing stands at the fascinating intersection of artificial […]
The Scope Recently, we conducted a red team assessment for a large enterprise client where the scenarios allowed were to […]
Prologue In the previous blogpost, we reverse engineered a binary and extracted the password from within it. This binary however […]
Welcome to the part 4 of malware development .In the previous parts 1, 2-1, 2-2 and 3, we created a […]
In the previous parts 1, 2-1 and 2-2 of this series we created a binary that can connect to, and […]
In the previous parts of this blog series, I introduced the concept of writing a full-undetectable malware and about […]
Welcome to the second part of the malware development blog series. Here’s the link to Part 1. Given the length […]
If you are in cybersecurity, especially Red Teaming, writing a full-undetectable (FUD) malware is a great skill to have. Folks […]
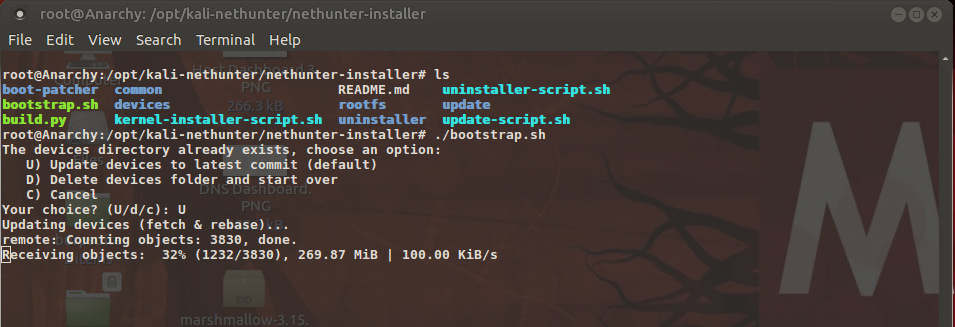
Part IV: Customizations – Custom Kernels and building Chroots This is the blog part 4 of building your custom Pentesting […]

Part I: The Prologue – Android rooting Background In the game, Watchdogs, the hacker ‘Aiden Pierce’ uses his cell phone […]